FourandSix2.01靶机
FourandSix2.01靶机
信息收集
1 | |
1 | |
1 | |
挂载 nfs
1 | |
奇怪的失败,查了以下,可能是需要 root 权限
1 | |
7z 压缩文件爆破
其中只有一个 backup.7z 文件,将其复制到本地路径下,然后使用 file 命令查看文件类型,使用 7za l 命令查看压缩包里的文件有哪些
1 | |
其中包含了一些图片和 ssh 的公私钥
1 | |
尝试解压但是需要密码,直接回车报错,那就使用工具爆破吧,原本想使用 rarcrack 但是爆破速度实在太慢,谷歌了一下,打算使用 hashcat 搭配
1 | |
hashcat 报错……搜了一下这个问题解决起来比较麻烦,应该是 VMware 的问题,尝试了几种方法都无效,那就在本机下载个 hashcat 来试试吧。
1 | |
爆破是有结果了……但是有个更抽象的问题,爆破出来的密码好像是错的,无法解压 7z 文件,换个工具 john 试试吧
1 | |
成功得到密码 chocolate,解压缩成功
1 | |
1 | |
私钥密码爆破
我们首先应该使用 file,xdg-open,binwalk(捆绑),exiftool(注释内容)来查看图片。
图片文件应该没什么问题,重点放在公私钥上,使用私钥登录试试
1 | |
私钥被加密了,那我们再来一次爆破
1 | |
好像不太好直接指定 john 的 format 参数,那就交给 john 自己来测试吧。再次遇到小问题,session 直接结束了
1 | |
不清楚造成的原因是什么,但是使用 sudo 来运行 john 命令就破解成功了
1 | |
ssh 登录
得到了密码,再次尝试 ssh 私钥登录
1 | |
提权
接下来考虑提权操作,首先进行 Getshell 后的信息收集,当前路径的文件收集
1 | |
passwd 文件
1 | |
没有定时任务?
1 | |
1 | |
doas 提权
etc 目录下确实没有定时任务的文件和目录,但是看到了一个特殊的文件,昨天刚刚遇到过这个提权手法 doas.conf
1 | |
emmm,不能说一模一样,但也是差不多
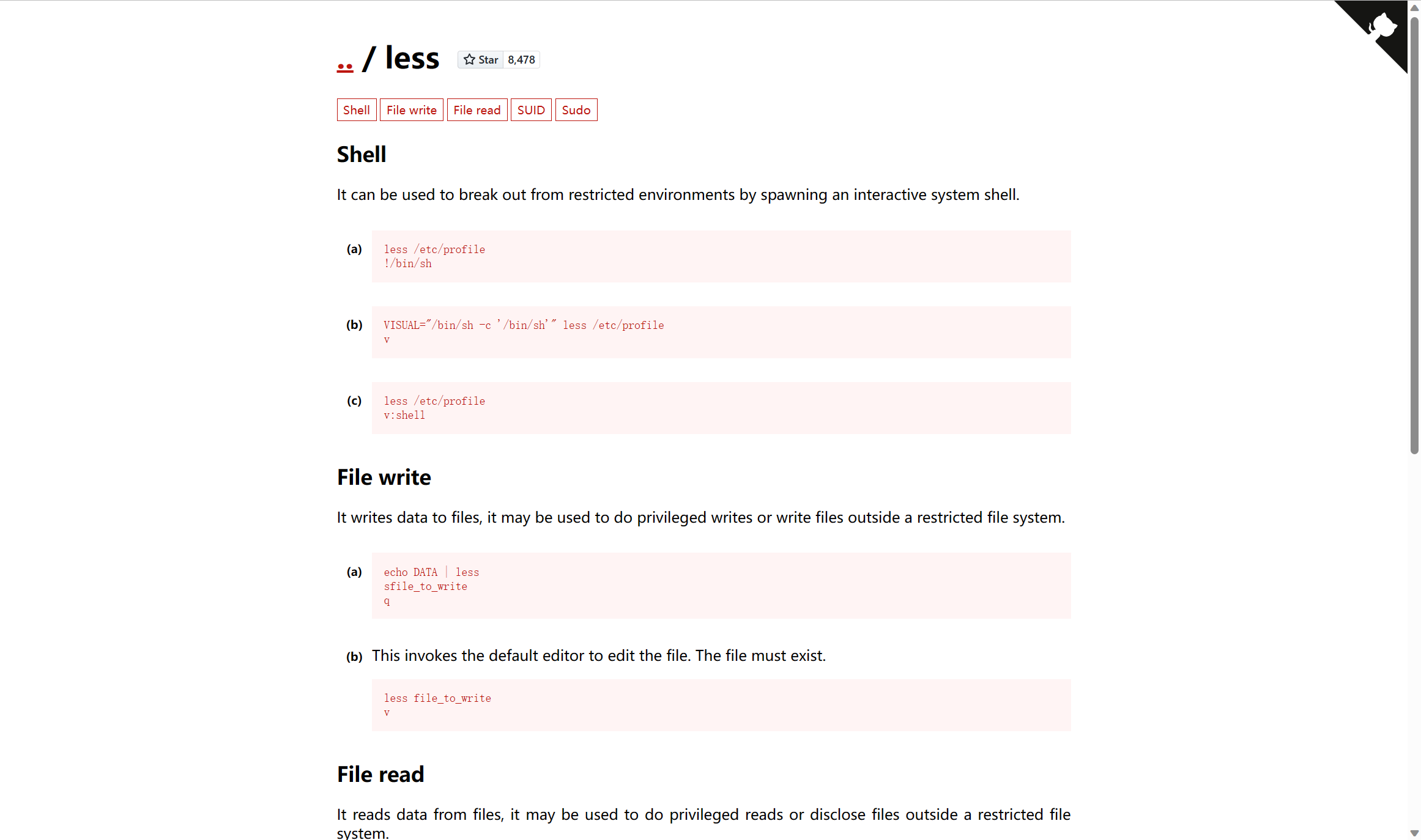
less 新启 shell
这里有新建 shell 的手法(v 是打开 vi 编辑器),我们按照 gtfobins 来新启一个 shell
1 | |
成功!
拾遗
挂载命令
1.目录事先存在,可以用 mkdir 命令新建目录
2.挂载点目录不可被其他进程使用到
3.挂载点下原有文件将被隐藏
1 | |
-t 指定文件系统的类型,通常不必指定。mount 会自动选择正确的类型。常用类型有:
光盘或光盘镜像:iso9660;
DOS fat16 文件系统:msdos;
Windows 9x fat32 文件系统:vfat;
Windows NT ntfs 文件系统:ntfs;
Mount Windows 文件网络共享:smbfs;
UNIX (LINUX) 文件网络共享:nfs
john 爆破工具
Linux 哈希爆破
JtR 破解的文件必须有特定的格式。要转换 passwd 和 shadow 文件,我们需要利用/usr/sbin/unshade 可执行文件。这需要超级用户权限才能执行。
1 | |
转化为 JTR 兼容的工具
1 | |
SSH 密钥密码破解
要测试JTR的SSH密钥密码破解能力,首先要创建一组新的私钥。注意:JTR没有破解文件本身(即生成的密钥中的字节数并不重要),JTR只是破解私钥的加密密码。
1 | |
接下来,您需要做的就是使用您的字典将 John the Ripper 指向给定文件:
1 | |
doas 命令的始末
来自维基百科的解释
doas (“do as”)是一个用来以其他用户身份执行指令的程序。系统管理员可以对其进行设置,赋予指定用户执行特定指令的权限。其为以 ISC 许可证许可的自由及开放源代码软件,可在 UNIX 与类 Unix 操作系统中使用。doas 是由 Ted Unangst 为 OpenBSD 所开发的,是一种更简单且更安全的 sudo 替代品
权限的定义皆编写于配置文件/etc/doas.conf中